Estimated read time: 4-5 minutes
This archived news story is available only for your personal, non-commercial use. Information in the story may be outdated or superseded by additional information. Reading or replaying the story in its archived form does not constitute a republication of the story.
PROVO — A new type of facial recognition technology designed by a Brigham Young University professor could make facial identification unlocking methods less vulnerable to hackers — and it isn't just for your phone.
By now, we've all heard of Face ID, and some of us might even have it on our phones. You hold the phone up to your face, it recognizes you and then lets you unlock your device.
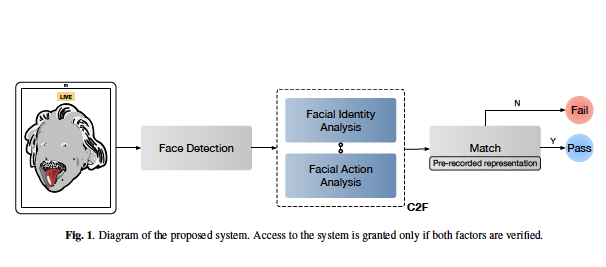
The technology does have downsides — like it could be used by another person pointing a camera at someone while the user is sleeping. BYU computer and electrical engineering professor D.J. Lee decided to add another layer of protection into the face identification technology to create a two-factor verification process. Instead of simply a face as the access code, it's a face doing a unique movement.
Unlike fingerprint and retina scans, the Concurrent Two-Factor Identity Verification requires users to do something unique with their face for the device to unlock. It can be a raised eyebrow, a tongue sticking out, or some combination of a few different things.
The camera will take a 1-2 second video of the person, turn it into dots on a map, and then each time the person creates that face it will identify the person.
"That's a very good feature to have to make sure it's intentional, so the user is basically aware and conscious," Lee explained.
In the preliminary study for the project, Lee and his Ph.D. student Zheng Sun created a dataset using 8,000 recordings they took from 50 participants doing a quick and unique facial motion or combination of motions.
The dataset analyzed which ones matched to show how accurate the technology was and found that it was working with more than 90% accuracy. The dataset was small, but the researchers think with a higher sampling, the number of positive matches will remain high.
To ensure privacy concerns are met, Lee said the camera wouldn't store the video initially taken but instead stores the unique data it converted the video into. It cannot be reverse-engineered back into a video of someone's face.
The technology isn't just for smartphones, either; it can be used for pretty much anything, Lee said. In fact, he has a lot of different application ideas from hotel room entry to starting your car.
"We don't want to compete with iPhone or mobile devices. We want to look at other applications," Lee explained.
As with any biometric option to security, another added benefit is there's no risk of losing a key or forgetting a passcode.
"It makes it easier that you just carry your face around, but then also it's better than the existing technology because you also have this unique facial movement that only you know," Lee said.
Adding the facial movement ID to something like personal banking — getting money at an ATM machine, for example — can also be more secure with the technology, Lee said.
"If you have a face, plus your facial movement, that's going to be harder to break in other than just the PIN code," he explained.
While the technology is still in its early stages of development, there are even broader applications that it could be used for aside from personal identification and security methods. The facial movement features could be used to develop communication features to help increase accessibility for those in the disability community, so a person could control a computer by moving different facial muscles.
Depending on what the technology is used for, the camera can be adjusted to make it either more strict or less sensitive. In a high-security area, it would probably be better to have a strict requirement where the facial movement needs to be precise and match nearly perfectly.
Right now, Lee and his team are working on commercializing the technology and looking for individuals interested in allowing the technology to be tested on their products. Lee filed a provisional patent this year for the technology, a customary practice for new ideas developed at the university.
In the end, Lee hopes the technology can be used in a variety of different ways to help make it harder for hackers to steal someone's identity or information.
"We were focused on solving ... unintentional identity verification," he said. "We use a password, and the password could be lost or stolen. And we use fingerprints and fingerprints sometimes could be fabricated, and also could be done unintentionally because, for example when you're sleeping. ... We want to find a solution that can address this big issue that is to make sure the identity verification process is intentional."