Estimated read time: 6-7 minutes
This archived news story is available only for your personal, non-commercial use. Information in the story may be outdated or superseded by additional information. Reading or replaying the story in its archived form does not constitute a republication of the story.
SALT LAKE CITY — The growing threat of ransomware is locking more and more people out of their digital photos, videos, word processing documents and other important computer files. Both PC and Apple users are at risk for the virus, and there’s no guarantee antivirus software will stop it.
Dr. Stuart Yeager’s computer at his Oakwood Chiropractic Wellness Center in Salt Lake City was one of the thousands infected by ransomware. His ordeal started when curiosity prompted him to check his junk mail folder.
“I just wanted to see this one email that came to me, and it said, ‘Invoice,’” Dr. Yeager said. “I thought it was harmless, you know. Who is trying to bill me?”
Dr. Yeager clicked the attachment.
“So, I opened the bill — nothing happened. It was like a little ‘poof’ kind of thing that happened,” he recounted.
But, something big did happen. The "poof" unleashed ransomware that went to work right away on encrypting the doctor’s computer files.
“All my word documents, my Excel files, the spreadsheets, word processing files, PDF files – those kinds of files that we use,” Yeager said.
Only when he restarted the computer did he learn why he couldn’t access those files any longer.
“I get this message on my computer that it was inflicted with a virus,” Yeager told KSL. “I had to pay this ransom and there was nothing I could do.”
“It’s not like robbing a bank where you go with a shotgun or pistol and you’re face-to-face to the potential of law enforcement,” said supervisory special agent James Lamadrid of the FBI.
Lamadrid said once your computer is infected with ransomware, it downloads the software necessary to encrypt the data on your hard drive and any other connected drive.
“In order to decrypt [your data], you have to have an encryption key,” Lamadrid said. “And, typically, for the infected victim to get that key, they have to pay a ransom.”
He said ransomware lurks in places we might not suspect, like online ads.
“Browsing, shopping websites might have some bad advertisers on,” he explained. “A bunch of shoe ads come up and could be loaded with malware to infect your computer.”
Legitimate sites like the New York Times, MSN and AOL have gotten hit by infected ads. An enabled popup blocker on your browser could protect you from clicking on one. Because once you do and the ransomware downloads, you may wind up trying to cut a deal with the devil lurking in cyberspace.
“Criminals know this is an area where it’s low risk, high yield in terms of what they do,” Lamadrid said. “You can do everything behind a keyboard, in a country thousands of miles away.”
Here's how it works:
If you pay the ransom, the anonymous crook who has locked your files may or may not send an encryption "key" to unlock them. The thieves almost always demand ransom payment be made in Bitcoin. It's a digital currency that's hard to trace, even for law enforcement.
Victims are paying ransoms by the millions. In 2015, over 2,400 people reported ransomware losses to the FBI totaling $24.1 million. Just in the first three months of this year alone, Americans have lost another $209 million.

“So, can you imagine what’s not reported?” asked Lamadrid. “Twice that? Three times that? We don’t know at this point.”
Ransomware infection can happen to anyone. The police department in Tewksbury, Massachusetts, paid a $500 ransom to unlock their arrest logs and other files. The city of Plainfield, New Jersey, had its servers crippled when an employee clicked an infected link in an email. The thieves in that case demanded $700. And recently, a Los Angeles hospital paid $17,000 to regain control of its entire computer system — including patient records — in the wake of a ransomware attack.
“What we find, most of the time, that it is those phishing scams to try to get you to click on something that looks official,” said the Utah Department of Public Safety’s commissioner, Keith Squires. His agency has teamed up with the FBI to investigate these cases.
“I see more and more criminals learning from each other on how they can be perpetrators and go after victims.” Squires said. “It’s a lucrative endeavor for the criminal and sometimes it doesn’t take the sophistication we think it would. It can happen to anyone.”
Even at KSL, we are not immune.
“I thought it was safe, it was the Adobe button — had the Adobe logo,” producer Jenniffer Michaelson said.
She had been tricked by what seemed to be a legitimate software update that popped up on her computer’s taskbar. She clicked it.
"I figured everything would run more smoothly, everything would work much better,” Michaelson said.
She called IT when her computer began running unfamiliar software.
“The second I started the virus scan, I noticed a lot more things happening,” remembered KSL network engineer Shawn Callaway. “As soon as I saw what was going on, I pulled the network cable from her PC to sever the network connections.”
Callaway’s gut reaction stopped the virus’ spread across KSL’s network. But, she did lose access to numerous files.
“It could have taken out our video,” Michaelson said. “It could have taken out the entire week’s newscast.”
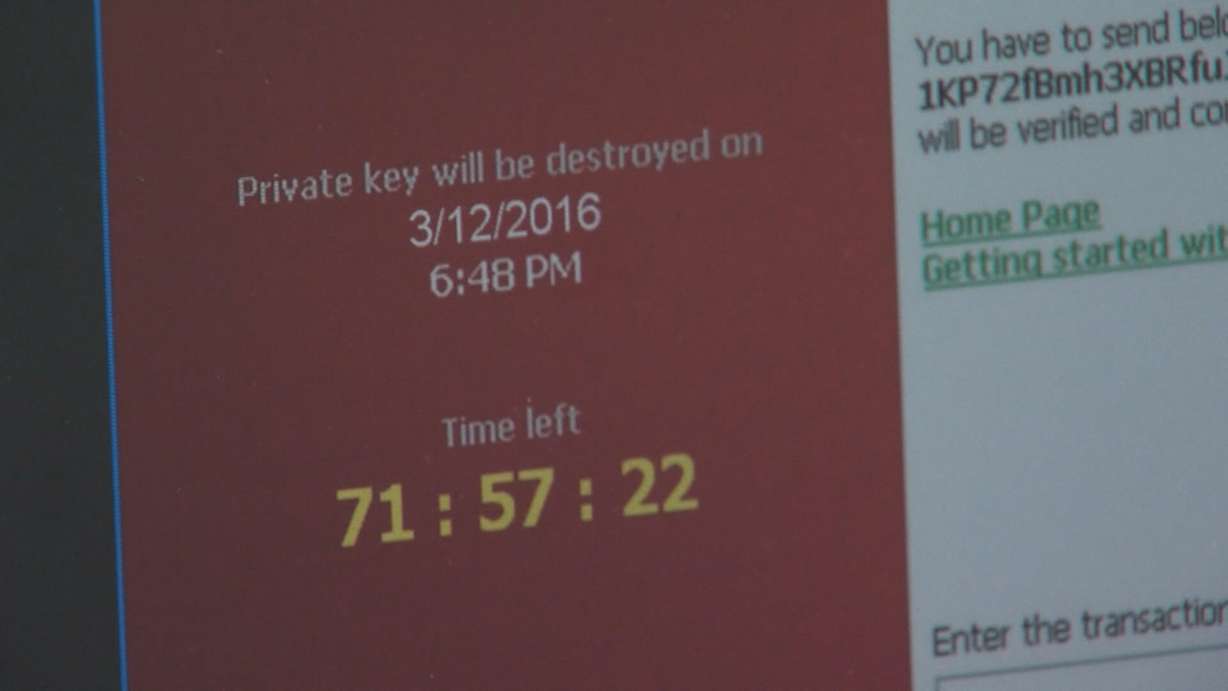
“It encrypts that file and leaves a little warning message in every single file folder that says ‘Your files have been encrypted. In order to get your files back, you must pay us in Bitcoin,’” Callaway said.
KSL did not pay the ransom.
“We knew that we had the proper back-ups and the proper fail safes so when we were held hostage by this ransomware. We didn’t have to pay it,” Callaway explained.
Dr. Yeager paid $500 to decrypt his files.
The thieves did not deliver on the encryption key. And several computer repair shops could not help him.
Dr. Yeager said while the virus did not infect his office’s record system, the files that were infected were personal and important to him to run his business.
Experts say backing up your computer regularly will help you avoid making ransom payments.
And check your backups.
"Even though you might think by pushing a button, you’re backing up data. Unless you check and try, you never know if it’s really there for you,” Lamadrid said.
And unplug your external or flash drive after you save your files. If they're plugged in the virus can infect them too.
“Just disconnecting it, something as simple as that can save you potentially tens of thousands of dollars," Lamadrid said.
The FBI also urges businesses to remind employees they should be suspicious of emails — especially with attachments — and of where they're surfing on the internet.
“Even though you may be expecting email from someone in your office or a family member, you should treat it as suspicious,” Lamadrid said. “Give them a call. It’s low tech, but you can save yourself a lot of heart ache.”
Contributing: Debbie Dujanovic
If you are a victim of ransomware, the FBI and the Utah Department of Public Safety wants to hear from you – they can provide guidance. You can start through the Internet Crime Complaint Center, www.ic3.gov.