Estimated read time: 2-3 minutes
This archived news story is available only for your personal, non-commercial use. Information in the story may be outdated or superseded by additional information. Reading or replaying the story in its archived form does not constitute a republication of the story.
SALT LAKE CITY -- If you've gotten an email from a company warning to be on the lookout for fraudulent emails, you're not alone.

Epsilon sends out billions of emails a year for more than 2,500 clients. The companies targeted:
- Citgroup
- Capital One
- Target
- Walgreen's
- Barclays Bank
- JPMorgan
- Chase Ameriprise Financial Inc.
- Best Buy
- TiVo
- Kroger
Millions of people are getting them, thanks to a security breach in which possibly millions of email addresses were stolen.
Someone hacked into the email system of a Texas-based company called Epsilon. It handles customer communications for hundreds of corporations. Epsilon sends out billions of emails a year for more than 2,500 clients. Those companies include Barclays Bank, JPMorgan Chase, Ameriprise Financial Inc., Best Buy, TiVo and Kroger.
The list of companies impacted by the data breach includes some of the country's biggest, like Citgroup, Capital One, Target and Walgreen's, which sent out an email alerting customers.
Experts are now saying you should watch out for "phishing" emails, which try to to con you out of more information.
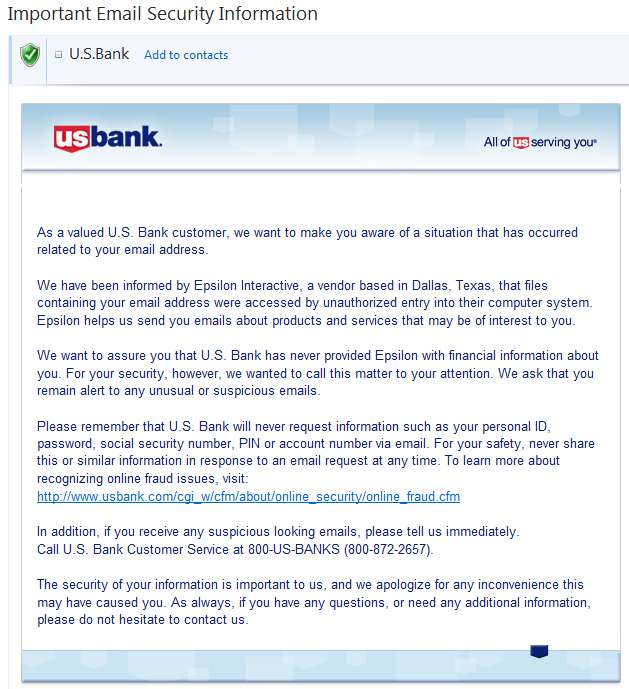
Local businessman and IT expert Pete Ashdown got a similar letter from US Bank -- which is interesting, because he's not a US Bank customer.
"It's shocking but not surprising," said Ashdown, president of X-Mission. "This kind of thing happens on the internet all the time. Security breaches are just a fact of life on the internet."
The biggest danger, says Ashdown, is that someone will use those stolen email addresses to try to convince people to give up their personal information over the internet.
"Somebody can fake that they are eBay or PayPal or your bank and ask for that personal information," Ashdown said. "It may look like a perfectly legitimate email, but it's not."
Matt Might, a professor of computer science at the University of Utah, agrees. "If the attacker has information like your real name, perhaps your phone number, they can make this email look a lot more authentic than your typical phishing email, and that's why they call if ‘spear phishing.' And this is going to enable spear phishing on the scale of millions."
Might says if you've gotten an email you're suspicious of, call the company.
To proactively prevent trouble like this, Might advises people to never use the same password for multiple websites.
"I would say in terms of defending yourself against a breach like this, have a different password for every website, absolutely," he said.
Also, there are password managers from online companies or in smart phone apps which help you keep track of all your many online passwords.
For more information and tips for protecting yourself, CLICK HERE.
Email: jdaley@ksl.com